Projects
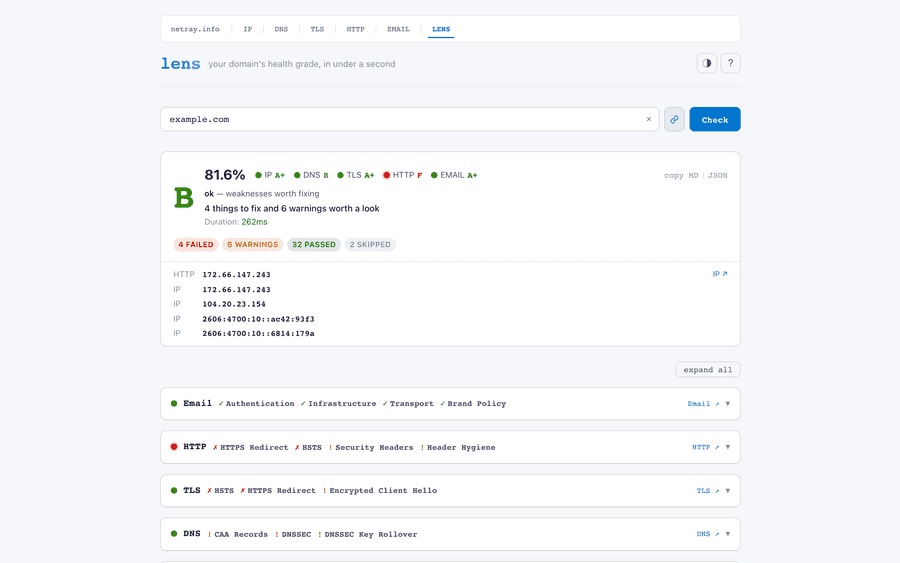
A network-intelligence suite — DNS, TLS, IP, HTTP, and email checks unified into a single A–F report, all built on one async Rust core.
A small suite of network-intelligence tools. Hand any of them a domain or IP and you get back a structured health report — TLS chains, DNS posture, security headers, IP reputation, email authentication — in well under a second, with raw JSON one click away for monitoring or CI. The homepage runs Everything is built on the same async Rust core: single-binary deployments, no runtime dependencies, consistent JSON contracts, OpenAPI docs throughout. Axum on the backend, SolidJS on the frontend. The DNS engine underneath is lens, the unified inspector: it fans every check across the suite and returns a single A–F grade with per-category breakdowns, streaming results back live as each check completes. Need to drill down? Each component also lives standalone at its own subdomain — DNS, TLS, IP — with HTTP header auditing and email probing tools in active development.mhost (also available as a CLI), and the unified scorer at the apex is lens — open to use, rate-limited, and ready to wire into your CI pipeline.
A single-command control plane for a local LLM stack on Apple Silicon -- mlx-openai-server, open-webui, and opencode under launchd, with profile switching and atomic rollback.
Running a local LLM stack on a 128 GB MacBook means juggling three daemons, a 70 GB working set, and the kind of macOS systems-programming that doesn’t fit in a Docker image. Under the hood: launchd plists live in Three slots in the default profile: GLM-4.7-Flash for build/code, Qwen3.6-35B-A3B for plan/knowledge, GPT-OSS-120B on-demand with a five-minute idle timeout. ~670 lines of bash, idempotent installer that owns the boring parts (sudoers, wired-memory limit, log rotation). Daily driver for one engineer — crib what’s useful.4lm is the single CLI that makes it behave — start, stop, switch profile, expose to LAN, diagnose — like brew services, but for an inference stack that takes a minute to flush from wired memory on shutdown.~/.4lm/launchd/, not ~/Library/LaunchAgents/ — so the stack never auto-starts at login. 70 GB of model weights is not something you want sneaking into the resident set before coffee. Profile switching is atomic: validate the YAML, swap a symlink, kickstart -k the backend, poll /v1/models for thirty seconds, roll back on timeout. expose lan refuses to bind to 0.0.0.0 without --confirm and prints the threat model first.4lm diag is the part I keep iterating on. It cross-checks the backend log against actual worker CPU and GPU power draw — if the log says “in flight” but every worker is idle, it surfaces the disagreement rather than picking a side. macOS gives you everything you need to debug a wedged GPU process — lsof, sample(1), powermetrics, ps -M — and none of it is in the GUI.
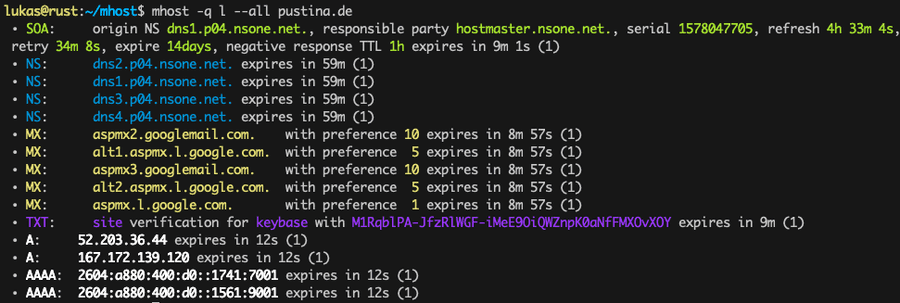
A DNS Swiss Army knife that queries 80+ resolvers in parallel -- lookups, discovery, linting, tracing, and an interactive TUI, all in one tool.
Ever wished But lookups are just the appetizer. For the explorers, there’s Everything outputs clean JSON for scripting, and the entire engine is available as an async Rust library with an ergonomic builder API — it’s the DNS engine behind Prism and the rest of the netray.info network intelligence suite.dig could do everything? Meet mhost — the DNS Swiss Army knife that makes DNS fun again. It fires queries at 80+ public resolvers in parallel and aggregates the results, so you get the full picture instead of trusting a single server’s answer. It speaks fluent UDP, TCP, DNS-over-TLS (DoT), and DNS-over-HTTPS (DoH) from Cloudflare, Google, Quad9, Mullvad, and more.mhost packs a whole toolkit into one binary: discover subdomains via CT logs, wordlists, NSEC walking, and permutation attacks. Lint your zone configs against 13 best-practice checks. Trace delegation chains hop by hop from the root servers. Check propagation across major providers after a DNS change. Diff records between nameservers or snapshots. Even verify live DNS against your BIND zone files — with non-zero exit codes for CI pipelines.mdive — a built-in interactive TUI with live sortable tables, drill-down navigation, discovery panels, and vi-style keybindings. Think of it as a DNS dashboard in your terminal.
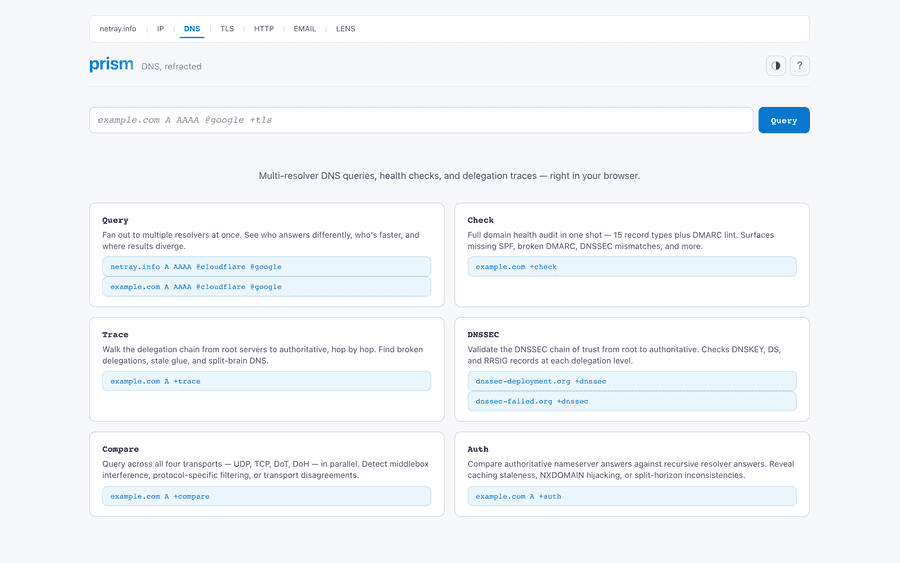
A browser-based DNS inspector that fans queries across multiple resolvers with streaming results -- part of the netray.info suite.
What if you could point your browser at a DNS problem and watch the answers stream in from every resolver at once? That’s Prism — a browser-based DNS inspector built on the Type a dig-inspired query like Prism packs six modes into one tool: Query to compare resolver responses side by side. Check to run a 15-record-type health audit with DMARC validation. Trace to walk delegation chains from root to authoritative. Compare to test the same query across UDP, TCP, DoT, and DoH. Auth to spot differences between authoritative answers and recursive caches. And DNSSEC to inspect keys and signatures. The frontend features a CodeMirror-powered query editor with syntax highlighting and completions, so crafting complex queries feels more like writing code than wrestling with CLI flags. Prism is the DNS component of the netray.info network intelligence suite. Try it live at dns.netray.info.mhost engine that ships as one binary, one config file, zero runtime dependencies.example.com A AAAA @cloudflare @google @quad9 +tls +dnssec and Prism fans it out across resolvers, streaming results back in real time via Server-Sent Events. No waiting for the slowest server — answers appear the instant they arrive.
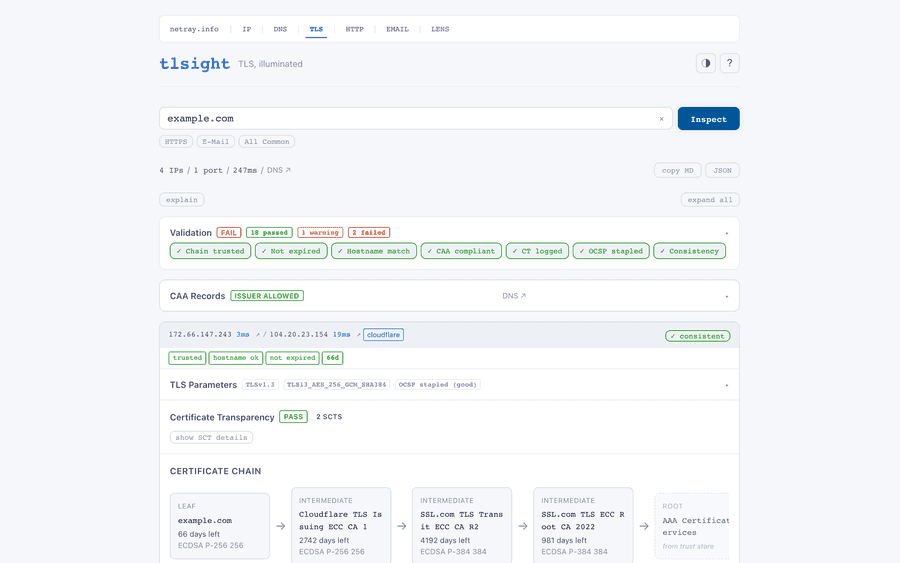
Full certificate chain inspection, TLS configuration analysis, and DNS cross-validation -- in one view.
Hand Under the hood, 13 graded health checks cover certificates, protocol configuration, and DNS alignment, giving you a structured pass/fail/warning assessment instead of a wall of text. Need to inspect multiple ports? Just say The whole thing is a single Rust binary with an embedded SolidJS frontend — no static file hosting needed. It exposes a clean JSON API with OpenAPI docs, making it easy to wire into monitoring or CI pipelines.tlsight a hostname and it comes back with everything: the full certificate chain from leaf to root, OCSP stapling status, Certificate Transparency SCTs, DANE/TLSA records, CAA authorization, HSTS headers, and DNSSEC validation — all in under two seconds. It even resolves every A and AAAA record and handshakes each IP in parallel, so you’ll spot that one CDN edge node serving the wrong cert before your users do.example.com:443,465,993 and tlsight checks them all simultaneously.tlsight is the TLS component of the netray.info network intelligence suite. Try it live at tls.netray.info.
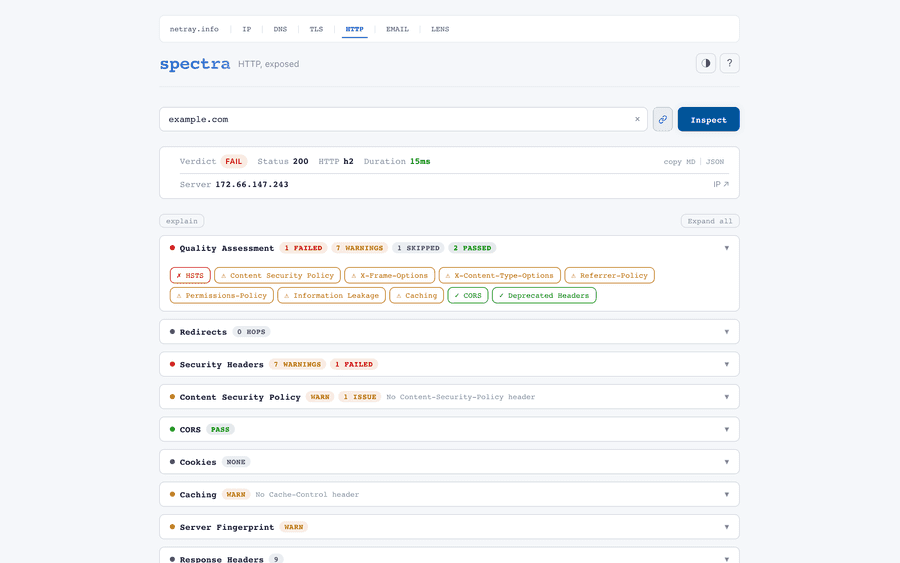
A three-probe HTTP header auditor — HSTS, CSP, CORS, cookies, CDN detection, the works — full report in under two seconds.
Most security-header scanners fire one request, scrape the response, and slap a grade on it. The HTTPS chain probe walks every redirect hop and picks apart every response header. The port-80 upgrade probe asks the boring-but-vital question: does plain HTTP redirect to HTTPS, on the same host, with the right status code? And the CORS probe sends Then comes the forensics: HSTS preload status, every CSP directive (with Every check scores Pass / Warn / Fail / Skip with an explanation; the overall verdict is the highest severity across them all. The whole inspection typically finishes in under two seconds. Browser, JSON API with OpenAPI docs, or one curl away: Live at http.netray.info — the HTTP component of the netray.info suite.spectra thinks that’s adorable. It fires three concurrent probes — because one is never enough.Origin: https://evil.example.com and watches what comes back — wildcard, reflection, or silence. (Reflected origin combined with Access-Control-Allow-Credentials: true is an automatic Fail. Yes, sites still ship that in 2026.)unsafe-inline, unsafe-eval, and wildcards called out by name), per-cookie verdicts (Secure, HttpOnly, SameSite, scope), full cache-directive parsing, CDN signature detection across Cloudflare, Fastly, Akamai, CloudFront, Vercel, Fly.io, BunnyCDN — including each one’s cache hit/miss state. Plus the wall of shame: fingerprinting headers (X-Powered-By, anyone?) and deprecated artifacts (X-XSS-Protection, Expect-CT, Public-Key-Pins) that do nothing useful and arguably make things worse.curl -s 'https://http.netray.info/api/inspect?url=example.com' | jq .quality
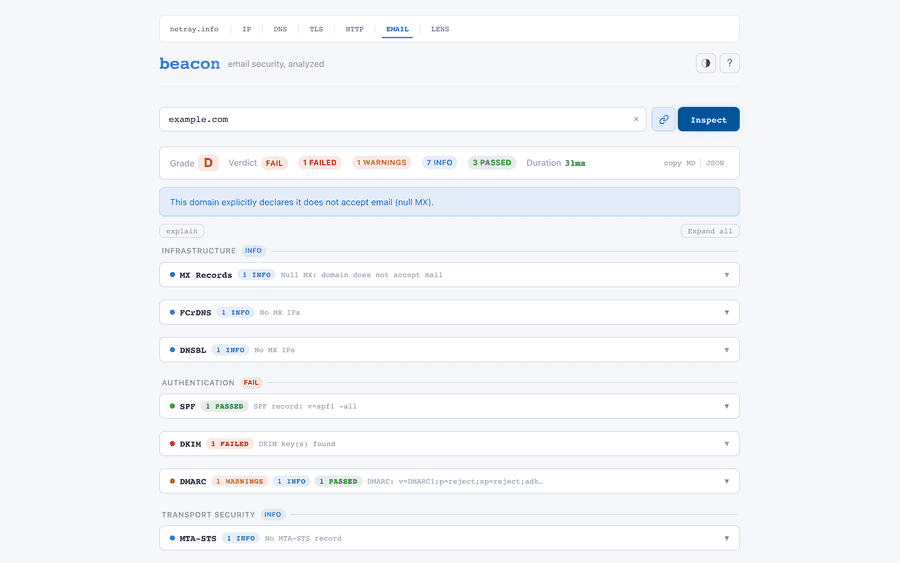
A DNS-only email-security inspector — 12 categories, A–F grade, streamed live, without sending a single mail.
Email security is a wall of acronyms, and most of them fail silently. The trick: it’s DNS-only. No probe mail, no SMTP handshakes, no greylisting, no false positives from a recipient that doesn’t exist. Just lookups, math, and a verdict. The kind of audit you can run a hundred times against your own domain without making your postmaster nervous. Results stream back live via Server-Sent Events as each category completes; a final summary event carries the A—F aggregate grade. Categories aren’t equal — a missing DMARC policy hits harder than a flaky BIMI logo, and the score reflects that. Cross-validation catches the bugs linters miss: an SPF record that whitelists a sender your DKIM key doesn’t, a DMARC Live at email.netray.info, or scriptable from the terminal: The email component of the netray.info network-intelligence suite.beacon audits 12 categories — MX, SPF, DKIM, DMARC, MTA-STS, TLS-RPT, DANE, DNSSEC, BIMI, FCrDNS, DNSBL reputation, and cross-record validation — and grades them honestly.rua address on a domain that itself fails alignment, an MTA-STS policy that points at a host with no matching MX. The class of misconfiguration nobody writes unit tests for.curl -N https://email.netray.info/inspect/example.com
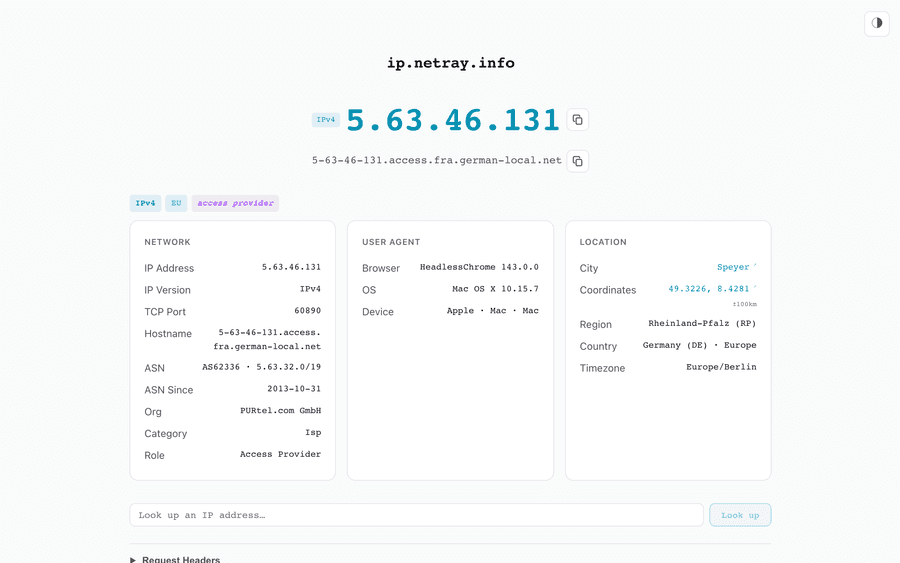
IP enrichment API with geolocation, ASN lookup, and cloud/VPN/Tor detection -- now powering the netray.info suite.
Written in Rust, it’s fast enough to handle batch queries and includes GeoLite2 data created by MaxMind, available from http://www.maxmind.com.ifconfig-rs started as yet another “what’s my IP address” service — but then it kept growing. Today it’s a full IP enrichment API that tells you everything about an address: geolocation, ASN, ISP, and whether it belongs to a cloud provider, VPN, or Tor exit node. It powers ip.netray.info, the IP component of the netray.info network intelligence suite.Features
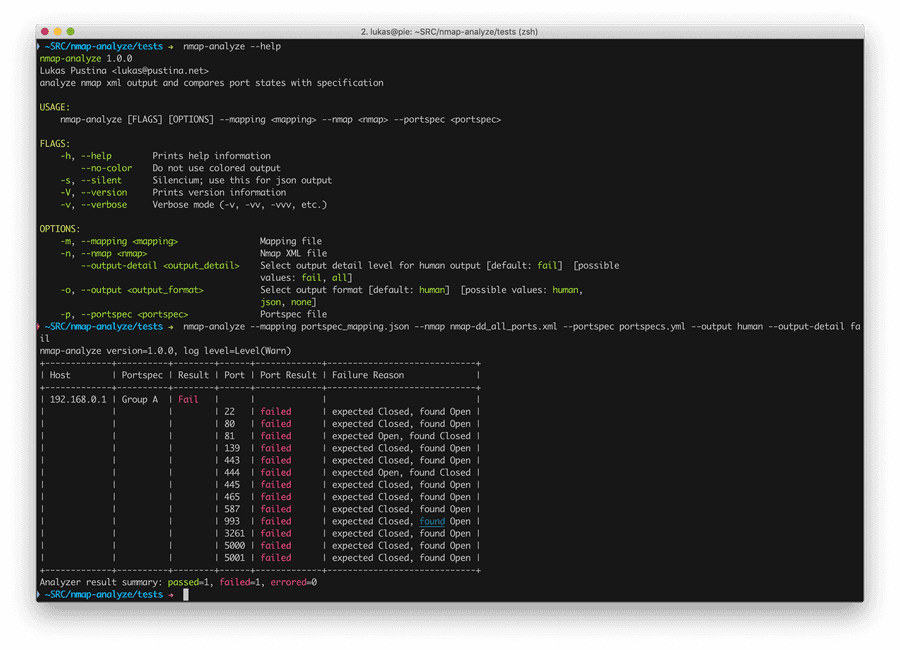
Analyzes and compares nmap scan results with port specification for easy verification of firewall and port filter configurations
nmap is a highly sophisticated and widely used port scanner. It scans a single host or a group of hosts for open TCP and UDP ports. This allows administrators to verify firewall and port filter configurations. nmap-analyze is a very simplistic tool that helps to ease this verification process. Basically, it takes nmap’s scan results as XML, compares these results for each host scanned with a specification, and reports all deviations. nmap-analyze supports both, human readable as well as JSON output. The later can be used for further post-processing.nmap-analyze needs three inputs: 1. nmap scan results in XML format, 2. a mapping of IP addresses to ports specifications, and 3. the port specifications. The mapping allows you to define groups of hosts that are mapped to the same port specification.